Security is a very sensitive topic these days. Data breaches, privacy violations, malicious attacks, etc. seem to dominate national and international news stories. As we become more connected, our data becomes more attractive and consequently more vulnerable to hackers. So, we need to take proper precautions to mitigate those threats.
Company databases are particularly susceptible to threats because data is the new oil. We rely on data to make important business decisions that ultimately impact revenue and overall business success. Therefore, we must take the time and effort to establish appropriate safeguards for our data resources.
DATA PRIVACY STANDARDS & REGULATION
In light of the fallout from Facebook's privacy breach and the impending General Data Protection Regulation (GDPR), data privacy warrants particular attention. Since extra data about people can be a liability when it comes to security, it's best to be conservative and only collect the data you need. Secure the data in your custom app according to industry standards and within your contact's expectations. For example, if you're in the healthcare field and you collect medical information from patients, you may want to audit your system’s architecture for HIPAA compliance. And you should always consider HIPPA before adding new data points to the database. If your data is accessible to third parties, you have to let your contacts know and confirm their consent before sharing their information. Whether you're engaging with folks in the US or the EU, be aware of the specific laws that protect different users/contacts and be sure you can adequately respond to questions about your data privacy procedures.
The Support Group's experienced System Engineers have compiled a list of some FileMaker security best practices. Ideally, these recommendations will complement your internal and/or industry security processes and requirements.
1. Create separate user accounts
We strongly recommend that each FileMaker user has their own individual account. We've seen many examples of organizations using one generic login for all users. Individual accounts do require more time and maintenance from an administrative perspective, but it provides mechanisms for accountability and audits. We understand that adding passwords might have been difficult on older versions of FileMaker Pro, but that is no longer the case.
2. Manage user privileges appropriately
All of your users do not require administrative access. You should clearly define roles and levels of responsibilities for each user and assign their access accordingly. And, when all of your users have their own individual accounts, you can adequately manage user privileges. This not only protects the integrity of your database, it also minimizes the potential for abuse.
Additionally, create a process for changing or terminating access when a user changes roles or leaves the company altogether. This is very important in theory and in practice.
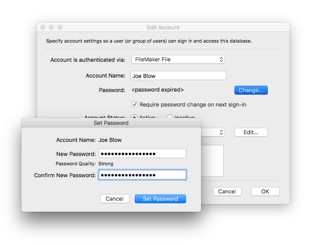
3. Specify password standards
You can reduce the administrative task of managing users by setting certain guidelines and processes for passwords. Firstly, passwords should be of a certain length and include special characters in order to prevent hacks. Secondly, you can establish automated password resets and expirations. So, if you forget to disable a user account, your system may eventually take care of that for you. FileMaker Pro provides tools to help assess password strength and enforce length and reset standards.
Please note, FileMaker access can be verified using external authentication if the application is hosted on FileMaker Server. This is great for users since they can use the same credentials to access all of their work systems. And, this is ideal for databases administrators and IT staff because they can control access to business systems from a central location and enforce strict password standards.
4. Assign passwords to default accounts
Did you know that when a new file is created in FileMaker Pro, a full access admin account is automatically created? Files are set to open automatically with the admin account and provide full access to data, layouts and schema. One of the first things you want to do with your database is require a valid account in order to access the file.
5. Control file access
FileMaker Pro makes it pretty easy to control what files users can access within a multi-file system. Rarely do all users need access to all of the files and its elements, i.e. layouts, tables, scripts, reports, etc., within an application. Rather than manually creating accounts for each file, FileMaker Pro facilitates the process for multi-file security with a suite of security script steps:
- Add Account
- Delete Account
- Reset Account Password
- Change Password
- Enable Account
- Re-Login
6. Automate the audit process
You should document when records are changed and by whom so that you can track changes back to specific users if there are any questions later on. And, timestamps will make it easy for you to restore a previous version of a record from a backup if the that ever became necessary. FileMaker Pro provides auto-enter fields to automatically document user login, record creation and record modification data. It's a very easy process that can save lots of time and frustration when items need to be reviewed.
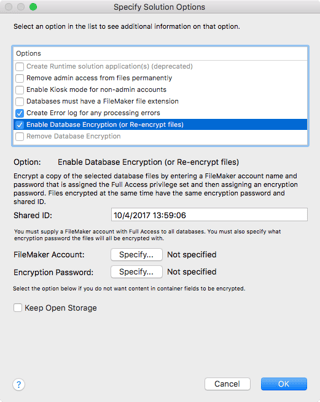
7. Encrypt sensitive information
Some applications require extra layers of protection. We do not recommend that you store sensitive customer information such as social security numbers and credit cards. But, if you must store sensitive information you should encrypt the data, during transmission and while it is stored. Using the Developer Utilities in FileMaker Pro Advanced, you can quickly and easily encrypt a database file. When you encrypt a file, you basically set up a password or key, that will be used to decrypt the file and make it accessible to appropriate users. Review the encryption options that are available in FileMaker Pro and make sure that you are using as many of the features as possible.
Be sure to secure the key because there is no way to recover it if it is forgotten.
8. Secure your data in flight
FileMaker Server has built-in Secure Sockets Layer (SSL) capabilities, which can be enabled on the Security tab of the Database Server section of the Admin Console. SSL certificates are actually required for FileMaker server. SSL protocol encrypts data between the server and the client - FileMaker Pro, FileMaker Go, FileMaker WebDirect or your Web Publishing engine. Please note, enabling SSL within FileMaker Server is for test purposes only. You must import a signed certificate from a certificate authority that matches your specific server name or DNS name in order for it to work in production. This is an advanced security mechanism so you may want to talk to your FileMaker developer about how to configure this properly.
9. Schedule regular database backups
Have you ever lost your phone, and by extension, your contacts, email, photos, etc.? It can be very debilitating if you have no way to restore the data. Needless to say, you should have a prescribed process for partial and full backups of your database. Regularly scheduled backups can protect you in the unfortunate event that your data is lost or corrupted. In addition to local storage, you should have a process for off-site backup and storage in case of a sudden disaster.
We can actually dedicate an entire blog post to just backup procedures so stay tuned for that.
This list of best practices is by no means comprehensive. These are just some basic suggestions to protect your application and avoid common security threats. Feel free to contact us to learn more about FileMaker security configurations or discuss customized recommendations for your application.
Find more custom application Developer Resources.